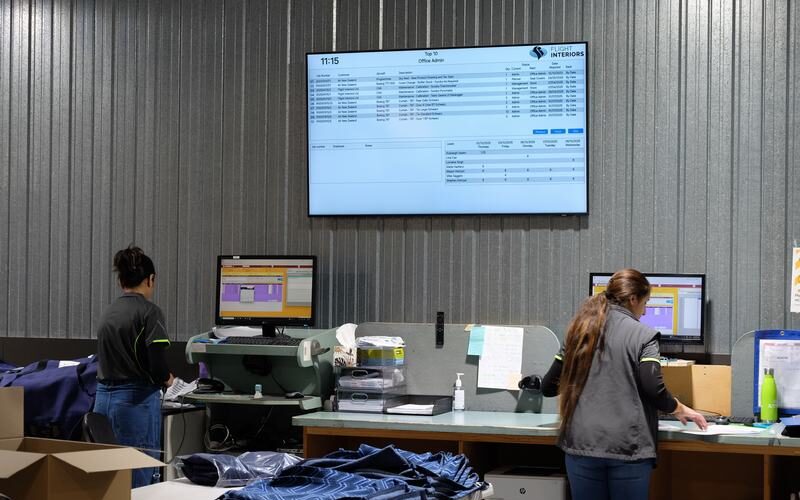
You might think an air traffic controller is a busy job. Imagine tracking every seat on every flight for an entire airline. We’ve collaborated with Flight Interiors to help them keep Kiwi flyers safe with an end-to-end software solution for their airline upholstery manufacturing business.

Hacked and Back
The hidden cost of a ‘Maybe’
Making a decision about the right level of cybersecurity investment for your business is unfortunately too often a case of looking at the costs, and picking the least scary one. Unless you’ve had the misfortune to be the victim of cyber crime it tends to be deprioritised, and a lot of money to throw at a ‘Maybe’. If you’re lucky, maybe it won’t happen, but if it does, how would that ‘maybe’ play out?
Swept under the cybersecurity mat
It’s a situation that many NZ businesses have experienced, and usually it’s very quietly dealt with internally. No one likes to share their experiences, but understanding what can happen, or how it can impact your business is critical knowledge that can help other businesses know what to look for, or how to respond. Knowing what could happen enables businesses to model out the implications, and assess their own security posture.
A Real Business. A Real attack.
We’ve recently helped a business triage a cybersecurity intrusion, where fortunately they’d made a reasonable investment in cyber security protection around their business data, even so, one of those classic vulnerabilities – human error, saw their system compromised.
We had worked with this business to develop a cybersecurity posture they felt aligned with their appetite for risk, relative to investment. Unfortunately, one of the risks turned into a reality, and they became victims of a cyber attack.
A Realtime Rundown
Here’s an insight into how that event played out, and fortunately they were able to overcome the setbacks
6.18am
ACIT were notified the off-shore servers of our client were going offline. This anomaly fell well outside their usual business hours. Immediately ACIT disconnected internet access to all connections except ourselves. Suspicious overseas connections from Asia were immediately terminated.
6.27am
System diagnostics were begun by the ACIT cybersecurity team. The servers had been encrypted using Microsoft’s Bitlocker technology and set to prompt for the Bitlocker key on startup.
7.20am
ACIT had scanned the access logs from Watchguard Endpoint protection looking back at the previous 12 hours. As with most systems there had been tens of thousands of access events. We identified irregular activity dating to 2.30am where a ‘known user’ had accessed the environment from an irregular location – India. Our ‘Known User’ was contacted and we verified his credentials had been compromised during a business trip.
Through forensic analysis we were able to trace the behaviours of the rogue ‘known user’ and saw they had elevated their permissions to administrator level. From there they had tried, and failed, multiple times to remove the Watchguard Endpoint protection hoping to access deeper levels of the database and our clients mission-critical data.
Unable to access this secure data they resorted to locking the system using Microsoft’s own Bitlocker – effectively changing the locks to the system – and leaving a simple text file on the admin desktop requesting a ransom, with contact details for payment.
7.55am
Having identified the source of the problem and the extent of the compromise, we were able to communicate to our customer what had occurred, and the implications for their business, with a plan of action to ensure their business continuity.
ACIT put forward a proposal for next steps, outlining the deep review of servers and systems they proposed, as well as a projected timeline for the analysis of firewalls, and logs to ensure any hidden issues were identified, isolated and eliminated. From this the client had clarity and the sability to communicate with their stakeholders.
ACIT moved forward.
11.30am – Business as Usual
Slightly over 5 hours from when the first symptoms of something irregular had occured, we pushed the servers live – cleaned and secure. The customer was operating as usual, albiet more aware of their close call. New protocols were implemented, including Multi Factor Authentication processes (MFA) on VPN access, with geo-locking of regions where the company did not operate.
Not all cybersecurity events are resolved in such a clear, linear way. Fortunately this business had invested in a system that delivered on what was promised, providing a fall back position, and minimal downtime. And, thanks to a well-established relationship and high levels of trust in us as their IT partner, with an understanding of their business and the potential threats, they had optioned a cyber security position that minimised the impacts of human failing.
If you’d like an assessment of your cybersecurity position, or to learn more we’re happy to help.